100% Effective data recovery software to completely recover deleted, formatted and lost files.
Quick Navigation:
BitLocker is a full-disk encryption solution you've heard of if you're a Windows user who's ever thought about protecting their data. BitLocker is a feature included in several Windows editions and is Microsoft's solution for full-disk encryption.
Most people would be horrified by having to replace their computer if it were lost or stolen. But if someone gained unrestricted access to the information stored on that device, that would be peanuts compared to the loss you would experience. A burglar can still access your system drive and all of its data by booting from an external disk, even if they don't have access to your Windows user account.
Completely encrypting the device so that no one but you or someone with the recovery key can access its contents is the best defense against that terrible scenario.
How does BitLocker work?
BitLocker's approach to achieving this goal is ingenious. You can encrypt the disk and keep the key somewhere other than on the disk itself to solve this problem.
TPM chips are now standard on most new motherboards. Decryption keys are kept in the TPM. The Trusted Platform Module (TPM) is accessed at the device boot-up to retrieve the decryption key. Because the key is stored in a different location than the main memory, the data will remain secure even if the drive is stolen. The TPM was developed specifically for use with the specified motherboard.
A TPM can be installed on a motherboard, but if yours doesn't have one, you can still require a password at startup by adjusting some settings. But doing so would negate the encryption's intended purpose, as the password must be stored on the disk. Alternatively, you might use a USB flash drive as the key. The USB disk with the encryption key must be attached to the computer before it will boot.

How long does BitLocker's first encryption take?
BitLocker encryption is performed invisibly in the background while the user keeps working, although the time it takes to complete depends on the encrypted drive, size, and speed. Scheduled encryption runs may be preferable for large enterprises because they can take a long time to complete, and the drive will be less likely to be used during the encryption process.
When BitLocker is activated, users can have the entire drive encrypted or just the data that is now being accessed. Sometimes, encrypting only the currently utilized data can be far quicker on a brand-new hard disk than encrypting the entire drive. When enabled, BitLocker will encrypt files on the fly as they are saved, making it impossible to keep an unencrypted file accidentally.
How to use BitLocker?
BitLocker is turned on automatically. However, if it is disabled, Manage BitLocker can be accessed using the Windows search bar. If BitLocker has been installed, the option to activate it will be available in the device's settings menu. Alternatively, you can turn off BitLocker, save your recovery key, or temporarily suspend protection.
Windows checks system settings after BitLocker activation. Users must create a password whenever they access their PC or drive. Select Recovery key settings. After selecting Next, the user can encrypt how much of their drive. Two-volume encryption can encrypt used disk space or the entire drive. Encrypting the entire drive encrypts all storage capacity, including vacant space, while encrypting used disk space encrypts only data.

The user can conduct a BitLocker system check after clicking on this to make sure BitLocker can access the recovery and encryption keys before encrypting anything. After the system checks, the BitLocker Drive Encryption Wizard restarts the computer for endpoint encryption. User sign-on and device registration to an AD domain provide protection.
Search for Manage BitLocker in Windows Search, choose the option, and switch off BitLocker to decrypt files.
What hardware does BitLocker need?
A Trusted Platform Module (TPM) chip is the primary hardware needed to facilitate BitLocker Device Encryption. The device must also be compatible with Modern Standby.
Almost all modern devices built from the ground up for Windows 10 will be compatible. Without exception, these specifications can be met by any device that runs Windows 11.
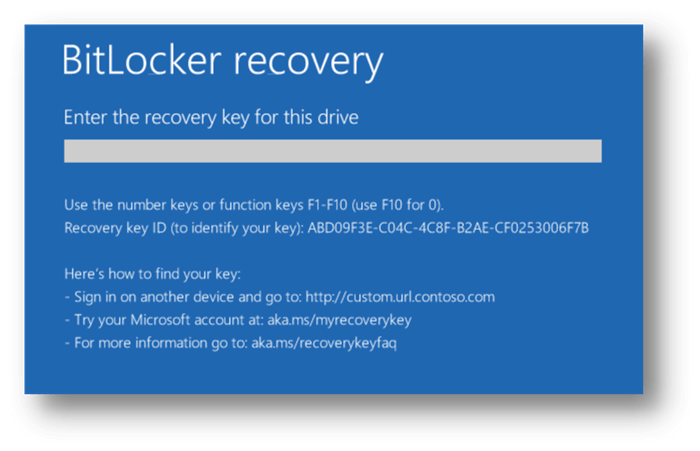
Signing into Windows with a device-authorized account unlocks your disk automatically. Booting from a Windows 10 or 11 Setup disk or a Linux-based USB boot device will require a recovery key to access the current drive. If a firmware update changes the system in a way the TPM doesn't recognize, you may be prompted for a recovery key.
Conclusion:
Data security cannot be guaranteed unless the boot device is also protected. If you're looking for a secure storage solution, BitLocker is it. You may adjust the level of security and ease to suit your needs precisely because it is secure, convenient, and adaptable. BitLocker should be used to encrypt your boot device as it is the first and most essential line of defense against unauthorized access to your data.
Related Articles
Donemax Data Recovery

Hot Articles
- How to Install Windows 11 on Unsupported CPU(See What We Do)
- Everything About the EFI System Partition on Windows 11
- Guides on Windows 11 Checker, How to Use it
- What Should I Prepare for the Windows 11 Upgrade
- How to Enable Secure Boot for Windows 11(Complete Guide)
- How to Install Windows 11 from USB
- How to Improve Windows 11 Performance?
- How to Remove Password in Windows 11
- The Difference between Windows 11 and Windows 10| Windows 11 VS Windows 10
- Should You Upgrade to Windows 11? What Benefits of Windows 11?
Hot Donemax Products
Clone hard drive with advanced clone technology or create bootable clone for Windows/Mac OS.
Completely and easily recover deleted, formatted, hidden or lost files from hard drive and external storage device.
Certified data erasure software - permanently erase data before selling or donating your disk or any digital device.